Zeus malware is back with a vengeance. A spin-off of the banking trojan, now with revamped espionage capabilities, was recently discovered by security researchers.
It’s called Terdot, a trojan that’s been active since mid-2016 and highly customized to conduct (MitM) man-in-the-middle attacks to intercept any traffic on an infected computer. The malware was also designed to inject HTML code or spyware into visited pages, steal banking credentials and credit card information. Commonly targeted websites include the Bank of Montreal, Banque Nationale, Desjardins, PCFinancial, Royal Bank, Scotiabank, and many other Canadian institutions.
Terdot wants more. The Zeus-derived banking trojan is out to get social media and email accounts.
Targets include popular social networks Facebook, Google Plus, Twitter, and YouTube, whereas the banking trojan could even post on the infected user’s behalf. Google’s Gmail, Microsoft’s live.com, and Yahoo Mail are among the afflicted email service providers. This new focus has the potential to make Terdot an extremely powerful cyber espionage tool.
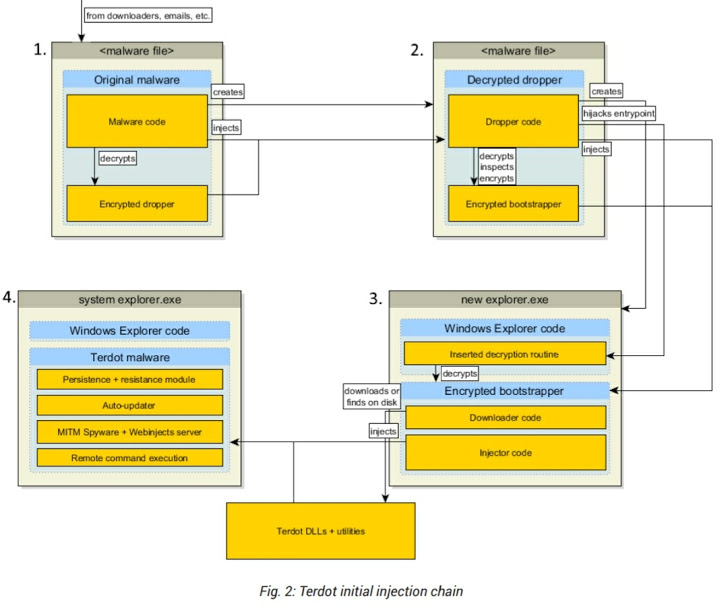
Bitdefender researchers have observed Terdot in malicious emails bearing a fake PDF icon. When clicked, obfuscated JavaScript code is executed to download and run the malware. Terdot is also delivered mostly on websites compromised with the SunDown Exploit Kit. Utilizing a complex chain of droppers, injections, and downloaders, Terdot evades detection as downloads are done in installments.
Terdot can then successfully intercept and modify any data victims send to their bank or social media account in real-time. Not only that, the banking trojan can spread itself through posting fake links on other social media accounts. It’s interesting how the malware apparently skips on gathering data from VKontakte, Russia’s largest social media platform, which somehow hints the actors behind the new variant may be from Eastern Europe.