If you have a business computer network, then you know that there’s all sorts of valuable information there. You might have employee information, trade secrets, and all manner of other sensitive data. You always need to watch out for cyberattacks, which is why you must invest in various security measures.
What we’re going to speak about today, though, are DNS attacks, which is a specific kind of cyberattack. We’ll also go over some things you can do to prevent them.
What Exactly is a Domain Name Server?
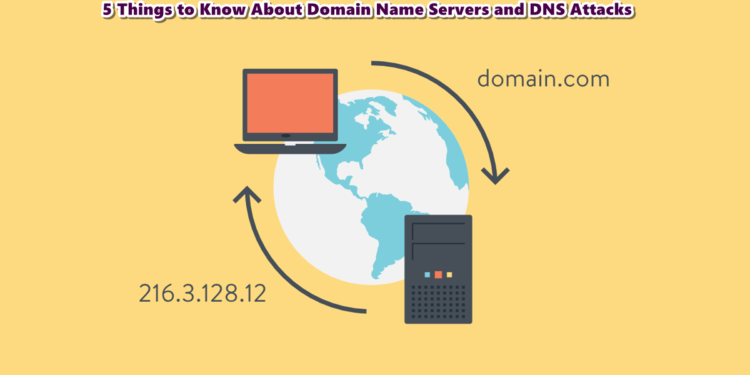
Before we dive into how you can protect DNS against attacks, you should understand what DNS means. DNS is:
- A decentralized, hierarchical naming system
- For internet-connected resources
Many tech-people call DNS the “internet phonebook.” The three letters stand for domain name system.
The DNS is a way to keep track of information. There are millions of internet-connected devices at any given time, including mobile phones, digital cameras, eBook readers, wristwatches, etc. DNS keeps track of information that you can then associate with each of these entities.
What is a DNS Attack?
As we mentioned, a DNS attack is a particular cyberattack form. A cyberattack is:
- When an individual or entity tries to gain unauthorized access to your computer or network
- A potentially harmful event that can cost companies millions
A cyber attacker might go after your device or network because they want to steal or destroy something. They might want to alter something as well. They may hope to expose your sensitive data to a broader audience than whoever you want looking at it.
As for a DNS attack, that is an occurrence where the attacker exploits domain name system vulnerabilities and gets into your network or device that way. There are all kinds of different attacks that fall under this more general banner.
What Are Some Different Kinds?
There are many different DNS attack strategies that hackers have devised, each more devious than the last.
For instance, there is what admins call protocol abuse. This is where an attacker uses the DNS in a different manner than what you intended for it. They can then bring about data exfiltration or implement phishing attacks.
There are also slow-drip or stealth attacks. This is where the hacker goes after the DNS with low volume requests that can cause outgoing query-processing capacity exhaustion. This could cause a server to crash or degrade.
One more example is the exploit attack. This is where the hacker identifies and exploits DNS protocol bugs or vulnerabilities. They might systematically comb through your DNS services operating system till they find a weakness, and then they break in through there and cause havoc.
Why Do Hackers Engage in DNS Attacks?
Hackers might have many reasons for staging a DNS attack, or any other cyberattack form, for that matter. They might have a grudge against your company. Maybe they don’t agree with some of your policies or the way you do business.
Maybe they’re a disgruntled employee with an ax to grind. Perhaps they’re doing it for profit. Some hackers will steal your trade secrets and try to ransom them back to you.
Still, others are anarchists or thrill-seekers who revel in taking down prominent business networks. Some hackers might work for foreign governments, and they’re going after your company because they want to destabilize the country.
A hacker’s motivation rarely matters, though. What’s more important are the security protocols you put in place to stop them.
How to Stop DNS Attacks
You can implement several methods to deter DNS attacks or make them more difficult for hackers to enact successfully. The most obvious way is to hire a company to do a thorough overview of your DNS practices.
Because this is an area that many hackers use to try and attack your network, numerous companies have sprung up that can overhaul your security protocols and suggest new best practices.
If you think you have a handle on it yourself, you can do things like configuring your DNS to be extra secure against cache poisoning. You’ll need to randomize the query ID and use a random source port. You can also keep your resolver protected and private, and you should restrict its usage to your network.
If you are at all uncertain about how best to protect your DNS from cyberattacks, reach out to a cybersecurity firm. They can take a close look at your setup and make some suggestions you should find helpful.